This Camio User Guide covers:
- Overview of Camio with AMAG
- Mapping cameras to AMAG readers
- Camio Setup for AMAG
- InfoSec Q&A
Download Camio AMAG gateway package for docker: https://storage.googleapis.com/camio-integrations/camio-amag-package.zip
Overview of Camio with AMAG
Fast visual verification and tailgating detection
Camio enables fast search and alerts on events like tailgating and entry unlocked. Read more at https://camio.com/tailgating.
Camio counts the number of people that pass through the door to compare that number to the actual number of AMAG access granted events. If those counts don't match, then the video is annotated with "tailgating" unauthorized access. This video illustrates tailgating detection as the floor plane tiles turn red when the second person enters after only one access granted event:
Works with existing cameras
Setup takes less than 15 minutes. Each camera is mapped to the AMAG reader so that events from those readers annotate the video from that camera. You configure the on-premise AMAG Proxy with the credentials required to subscribe to AMAG access control events.
Mapping cameras to AMAG readers
The first step is to associate your AMAG readers with any cameras that can see the doors controlled by those readers.
- Generate your Camio Authorization token to be used by the AMAG Proxy to annotate video with incoming access control events.
- Sign-in as the Camio account manager and press the Generate button at https://camio.com/settings/integrations/pacs
- Copy the token immediately after you generate it, since you will not be able to retrieve it again later.
- Paste the token into your camio_config.yaml as camio_auth_token: {{CAMIO_AUTH_TOKEN_HERE}} value.
- Find your AMAG server, database, and user credentials and place them in the associated fields within the amag_config.yaml and the amag_user.yaml files.
- Select the AMAG Reader from the dropdown list next to each camera that has a view of the people entering the door associated with that reader and press Save.

Camio Setup for AMAG
The AMAG Proxy subscribes to AMAG access control events in order to annotate the video associated with each event.
AMAG Proxy Installation
The AMAG Proxy runs as Docker containers on any host machine that can access the AMAG server. If your firewall restricts the sites contacted, then please see Firewall Rules.
AMAG Proxy Configuration Files (yaml files)
The AMAG Proxy's configuration is determined by yaml files. Upon first startup of the AMAG Proxy, these yaml files are encrypted and deleted so that secret credentials are never stored in the clear. To supply new option values, you must stop the containers, add the yaml files to the res directory, and restart the Docker Containers so that they read and encrypt the yaml files once again. See Updating Configuration Files.
|
Filename |
Description |
|
camio_config.yaml |
This contains your secret Camio Authorization token obtained from https://camio.com/settings/integrations/pacs used to annotate video. Example: CAMIO_CONFIG: |
|
amag_config.yaml |
This contains the non-secret information required to connect to your AMAG server. Example: --- AMAG_CONFIG: |
|
amag_user.yaml |
This contains your secret AMAG username and password required to access the AMAG server. Example: AMAG_USER: |
|
advanced_config.yaml |
These default values should be sufficient, but override any desired. Retain the query_filter, so that only recognized AMAG Events are sent to Camio. Example: --- ADVANCED_CONFIG: |
AMAG Event Filter
Descriptions:
- Entry Unlocked
- Granted Access
- Granted Access (Extended Door Time)
- Door Open
- Door Unlocked
- Entry Ajar
- Door Insecure
- Door Held Open
- Door Held
- Entry Forced
- Door Forced
- Door Open With Tamper
- Exit Open With Tamper
- Unmapped But Still Labeled:
- Access Denied
- Door Not Opened
- Wrong PIN
- At Wrong Time
- Unknown Card
- At Wrong Door
- Wrong Customer Code
- Unknown Fingerprint
- Valid Access At In Reader
- Floor Access
- Valid Access At Out Reader
- Door Reclosed
- Entry Timer Expired
- Entry Timer Reset
- Card Expired
- Access Requested
- Access Requested (PC door control)
- Door Closed With Tamper
- Exit Closed With Tamper
- Door Closed
- Door Closed
- Door Forced Clear
- Door Held Clear
- Door Exit Button
- Door Lock Jammed Clear
- Door Lock Jammed
- Door Lock Held Clear
- Door Lock Held
- Door State Monitor
- Door Lock Monitor
- Door Free Access
- Door Unlocked
- Allowed
- Accessed
- Pre Held
- Access Denied
- Wrong PIN
- Unknown Event
- IP Camera Offline
- IP Camera Online
- Camera Restarted
- Tailgating
Installing on Linux
- Download and install Docker by following the steps for your Linux distribution from: https://docs.docker.com/engine/install/
- Download and install docker-compose by following the steps from: https://docs.docker.com/engine/install/
- Download the AMAG Proxy run package from: https://storage.googleapis.com/camio-integrations/camio-amag-package.zip
- Unzip the package
-
unzip camio_amag_proxy.zip
cd camio_amag_proxy
cd res
ls -l - Update the configuration files with Camio and AMAG information
- Once the config files have been updated, from the dist directory run the Camio container
-
docker-compose -f docker-compose.yaml up -d - If you want to run the container in foreground, then remove `-d`
-
docker-compose -f docker-compose.yaml up - The AMAG Proxy containers are now running. You can use Docker commands to watch stats and logs whenever required.
Installing on Windows
- Download and install Docker Desktop (which also contains docker-compose) by following the steps from:
https://docs.docker.com/docker-for-windows/install/ - Download the AMAG Proxy run package from: https://storage.googleapis.com/camio-integrations/camio-amag-package.zip
- Unzip the package, and enter into the camio_amag_proxy directory
- Update the configuration files with Camio and AMAG information
- Once the config files have been updated, from the dist folder run the Camio container
-
docker-compose -f docker-compose.yaml up -d - If you want to run the container in foreground, then remove `-d`
-
docker-compose -f docker-compose.yaml up - The AMAG Proxy containers are now running. You can use Docker commands to watch stats and logs whenever required.
Updating configuration files
- When you need to update the configuration files, you first need to stop the containers by running
-
cd camio_amag_proxy/dist
docker-compose down - Wait for the containers to stop, and then add the new configuration files in the res directory.
- Note that due to encryption and security, all of the existing configuration files in clear text will not be present in the res directory, so you will need to add fresh new configuration files in the res directory.
- After adding the new configuration files, restart the containers by running:
-
cd camio_amag_proxy/dist
docker-compose -f docker-compose.yaml up - The AMAG Proxy containers are now running with the updated configuration files. You can use Docker commands to watch stats and logs whenever required.
AMAG Proxy Host Hardware Requirements
The CPU and RAM required of the host machine that runs the AMAG Proxy Docker containers varies with the maximum throughput of access control events. This guide covers common volumes:
|
Max Event Rate |
CPU Cores |
RAM |
|
100 events/second |
1 |
300 MiB |
|
1,000 events/second |
2 |
400 MiB |
|
10,000 events/second |
2 |
400 MiB |
Firewall Rules
During the initial docker setup (docker-compose up -d) will need access to these servers:
- gcr.io
- storage.googleapis.com
- dockerhub.com
During operation ,the Camio AMAG Gateway will need access to these servers:
- https://camio.com/api/integrations/pacs/webhooks
- https://camio.com/api/integrations/pacs/devices
- https://us-central1-camio-test.cloudfunctions.net/test_callback_integration_amag
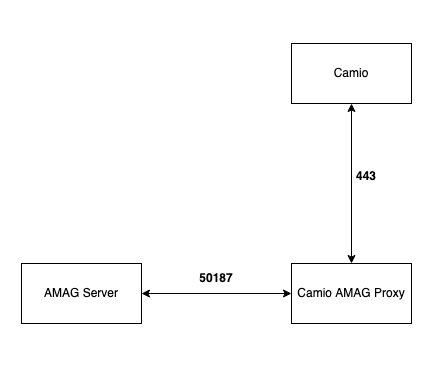
Ports
The Camio AMAG Gateway uses ports:
- 443 to talk to the Internet servers above
- 50187 to talk to the AMAG server (or the port you chose for your AMAG server)
During the initial docker setup (docker-compose up -d) the Camio AMAG Gateway will retrieve the docker images using port 443.
During operation, the Camio AMAG Gateway uses two docker containers that talk to each other on a docker bridged network using ports 6379 and 8080. But those ports aren't open on the Local Area Network.
The port used to make requests of the AMAG server will vary based on your network settings of your AMAG system, but the default port found in amag_config.yaml is 50187.
InfoSec Q&A
Q: How does the Camio AMAG Gateway connect to AMAG panels?
A: There is no communication with the AMAG panels themselves. The access control events are instead read from AMAG's SQL Server database via a read-only connection.
Q:What ports must be opened for the servers, and why?
The default port for the AMAG SQL Server database is 50187, but you can choose whichever port you configured for AMAG. That port is used for read-only query of the readers and access control events from AMAG.
Q: What information does Camio pull from the SQL database?
The read-only queries retrieve a) events and b) the list of available readers to be assigned to cameras. The events data look like this:
{
"badge_id": 100,
"company_id": 1,
"company_name": "My Company",
"device_id": 2,
"device_name": "AEPanel - fake reader 1",
"event_id": 1683438,
"event_text": "Granted Access [100]",
"event_time_utc": "2021-11-03T18:42:00.000000"
}
The Camio AMAG Gateway relays only these three Reader fields to camio.com:
- ReaderID
- ReaderName
- CompanyID
Q: How is the information being pulled AMAG?
An ODBC connection to SQL Server submits queries to retrieve events and readers.
Q: What is the security we are using?
The ODBC connection is established with username and password credentials supplied by the config file and connects on the Local Area Network without a secure connection like this:
sql_engine_url = (f'mssql+pyodbc://{self.username}:{self.password}@{self.sql_server}/'
f'{self.sql_database}?driver=ODBC Driver 17 for SQL Server')
Q: Which AMAG tables are accessed?
To list the Readers:
SELECT * FROM Reporting.Readers
To list the entry unlocked Events:
SELECT * FROM multiMAXTxn.dbo.viewalarmeventtransaction
----
For more information on PACS integrations see https://help.camio.com/hc/en-us/articles/4409969059732-How-do-I-set-up-a-Physical-Access-Control-System-integration-User-s-Guide- and https://help.camio.com/hc/en-us/articles/4409631039892-How-do-I-create-a-Physical-Access-Control-System-integration-Developer-s-Guide-
Comments